As of today, most businesses are seeing the value and success one can have when building an offshore team. However, the question of “Security” is still the top concern of most business owners regarding offshoring their processes.
In the past, there were horror stories about security breaches when it comes to having a remote staff which lead to questioning the security of their confidential data with their remote team.
While those concerns are valid, there are ways to reap the benefits of having an offshore team without worrying about confidentiality.
Here are some tips on how to find an offshoring provider that values cybersecurity:
1. Choose the safest business model
This is one of the most important steps when you start on building your Team. When you are starting to build your Team, you have options, such as getting freelancers, outsourcing your people, or building an offshore team.
In the case of using freelancers, it may reduce your operational costs. However, it is important to note that there is a higher chance that it will also expose your business to significant security risks.
Even with an NDA in place, there are many uncontrolled elements or threats to be worried about, especially if dealing with a freelancer from another country.
The same goes with an outsourced staff or team. In many cases, they do not abide by the standards of your company, but instead of their employers. How they keep your information safe might not be the same way as you do.
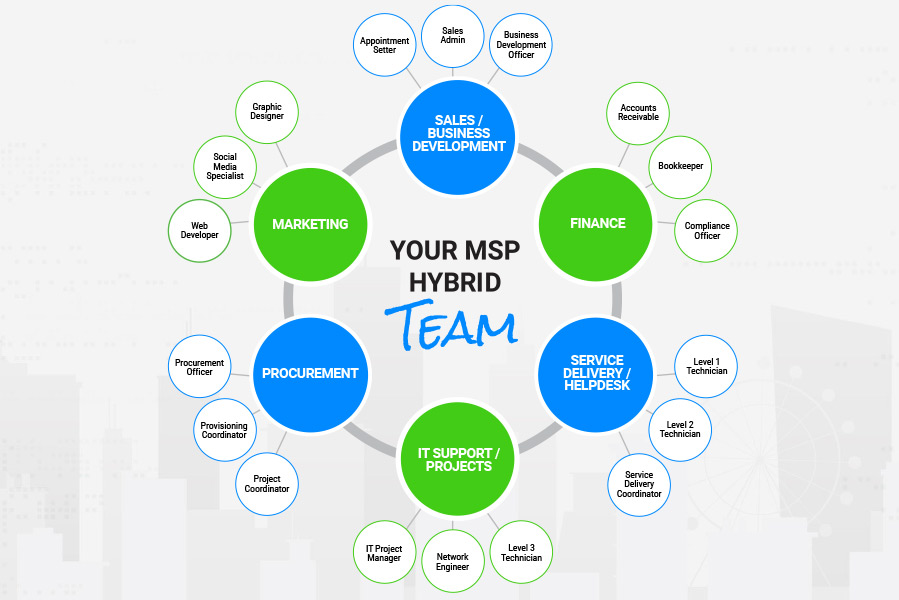
With a dedicated offshore team, it means hiring a handpicked group of individuals who are 100% part of your Team.
They are permanent, full-time employees who are just like your local team, except that they are based elsewhere. Implementing and monitoring cybersecurity processes and best practices are easily transmitted to your team.
2. Secure all applications and devices
When building a remote team, the IT infrastructure is important. When choosing an offshore staffing provider, here is a quick checklist of their minimum cybersecurity must-haves for their operations:
- Do they encrypt and install firewalls?
Installing security patches and updating the security software on all endpoints provides personal firewall, application control and anti-virus protection.
- Do they secure access to all company systems?
When working with a remote team, restrict system access to specific networks. And if any employee desires to log in from a different site, they can do so only once their network is authenticated. This mitigates risk and ensures the early detection of a hacking attempt.
3. Assess and engage safe cloud providers
Cloud computing is one of the most scalable and easy-to-set-up means of storing and accessing files. However, without the right security measures, files in the cloud can be accessed by those who do not belong to your company.
Here are some considerations:
- Ensure that frequent cloud security audits are performed in compliance with standards such as ISO 27001.
- The server rooms are secured with RFID (or better yet, biometric device)with no or limited access to the public.
When choosing offshore staffing providers, please know that not all offshore staffing providers are well-adept in the practices of cybersecurity.
Even if they do promise, the only way to prove that they “walk the talk” is if they are ISO 27001 certified.
We, at Techo Global Team, understand that cybersecurity is important to you. To show our commitment, we abide by the strict international standards of ISO 27001.
—————————————————–
If you are interested in exploring the possibility of building an offshore team, feel free to reach out to us by sending an email to [email protected] or use the form here.